Our Blog
6 Types of On Demand Auto Insurance and Who They Fit Best
For decades, personal auto insurance has been built around the annual policy. Fixed term. Fixed premium. Fixed assumptions about how often and how well someone drives. That model is now under sustained pressure.
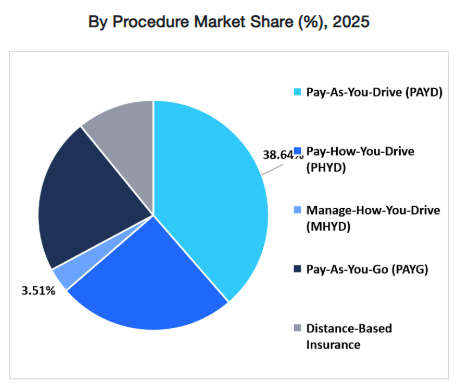
According to McKinsey, more than 40% of U.S. auto insurance customers express interest in usage-based or behavior-linked pricing models. Consumer expectations are shifting faster than traditional product cycles.
OEM ecosystems are embedding coverage at the point of sale. Mobility platforms are normalizing short-duration vehicle access. Urban consumers are driving fewer miles than pre-2020 levels in many markets, yet paying annualized premiums structured around older assumptions. On-demand auto insurance is emerging within this shift. But for U.S. P&C insurers, this is not a consumer trend story. It is a portfolio design decision.
Each on-demand model: whether temporary car insurance, usage-based auto insurance, telematics insurance, subscription car insurance, embedded auto insurance, or on-off activation, fits specific segments and distribution strategies. Each also requires disciplined underwriting, real-time servicing infrastructure, and careful compliance alignment across state regulations.
This article breaks down six distinct models, their best-fit segments, and the strategic implications insurers must evaluate before deciding where, and whether, to play.
What Is On Demand Auto Insurance?
On demand auto insurance refers to coverage that is activated, priced, or adjusted based on time, usage, behavior, or context rather than fixed annual assumptions. Instead of locking in a 12-month exposure period, the policy structure responds dynamically to how and when a vehicle is used.
In practical terms, this includes temporary car insurance for short durations, usage based auto insurance tied to mileage, telematics insurance driven by driving behavior, subscription car insurance bundled with services, embedded auto insurance offered at the point of vehicle purchase, and on-off activation models that allow policyholders to toggle coverage.
What distinguishes on-demand models from traditional personal auto is not simply flexibility, it is pricing logic and operational design. Premium is linked more closely to exposure data. Underwriting increasingly relies on real-time inputs. Servicing is digital-first. Proof of insurance, regulatory disclosures, and state reporting often must occur instantly.
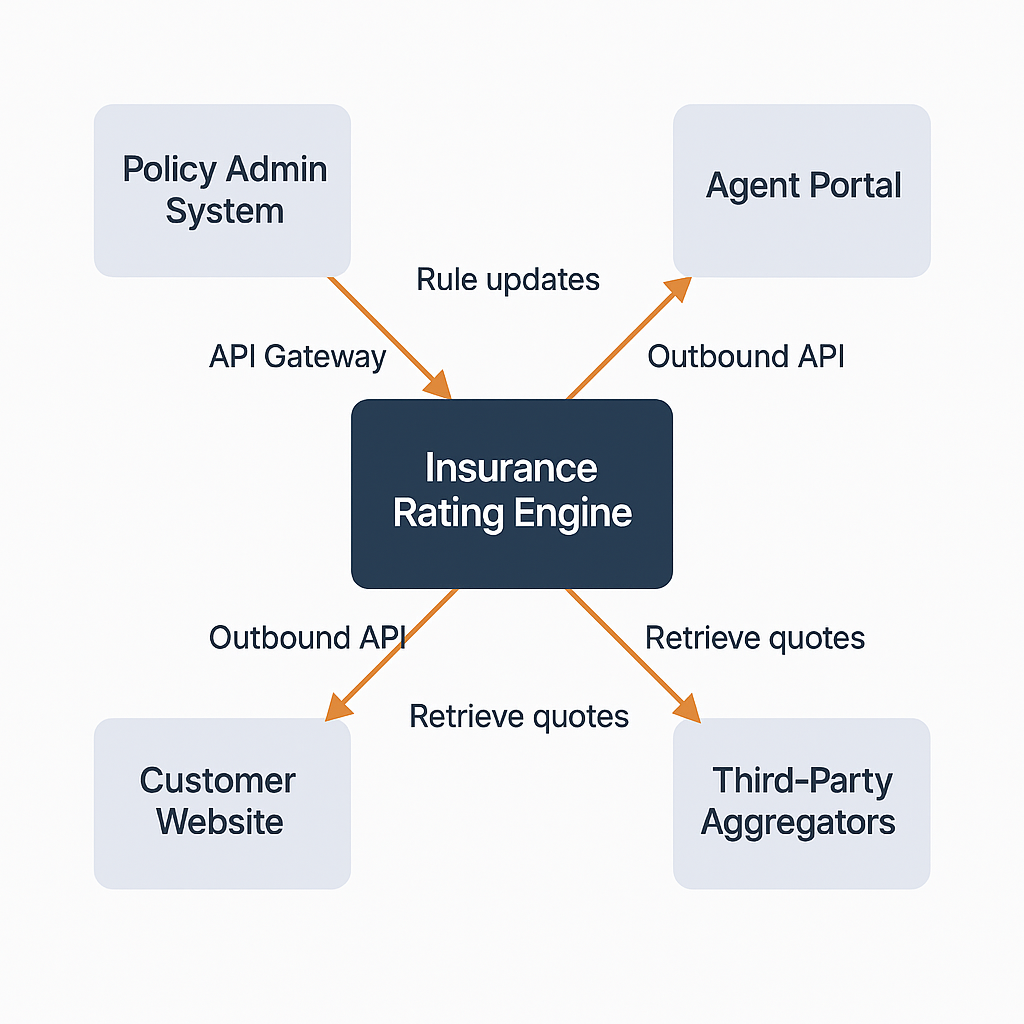
For U.S. P&C insurers, this introduces structural implications. Rating engines must support micro-duration logic. Fraud controls must operate at bind. Compliance workflows must align with state-specific rules on cancellation, cooling-off periods, minimum limits, and proof-of-coverage timing. On demand auto insurance is therefore less a single product and more a category of portfolio strategies built around responsive exposure measurement.
6 Types of On Demand Auto Insurance
1. Pay As You Need (Time-Based Cover)
Pay As You Need, or time-based cover is a form of temporary car insurance that provides protection for a defined short duration, typically hourly, daily, or weekly. Coverage activates for a specific time window and expires automatically at the end of that term.
Unlike a traditional policy that simply gets cancelled early, time-based on-demand cover is intentionally engineered for limited exposure. That matters because short-duration buyers are often selecting coverage around specific moments, which can create very different loss patterns than a stable annual book. Pricing therefore reflects compressed duration risk and higher variance, rather than spreading expected loss across a full-year premium base.
Best-Fit Customer Segments for Pay As You Need Model
- Borrowed car drivers
- Occasional drivers who do not maintain full-time policies
- Urban residents using vehicles intermittently
- Short-term vehicle access (weekend travel, road trips)
- Gig drivers during temporary activation windows
This model often appeals to digitally comfortable consumers who expect immediate coverage confirmation and proof of insurance.
Strategic Value for Insurers
Time-based cover can serve as:
- A low-friction acquisition channel for younger or first-time insureds
- A bridge product that converts short-duration users into annual policies
- A way to participate in non-owner or occasional-driver segments
- A defensive play against insurtechs specializing in temporary car insurance
For carriers with strong direct-to-consumer capability, this model can also reinforce brand relevance among mobility-first demographics. Strategically, it expands the addressable market without immediately committing to long-term exposure.
2. Pay As You Go (Mileage-Based Coverage)
Pay As You Go is a form of usage-based auto insurance where the premium is directly linked to miles driven. Instead of paying a fully fixed annual premium, the insured typically pays a base rate plus a variable per-mile charge.
Exposure is captured through verified odometer reads, app-based mileage tracking, or telematics devices. That data continuously updates the insurer’s view of exposure, so premium is tied to actual miles driven, not a static annual mileage estimate provided at underwriting. The result is a pricing model that adjusts with real usage patterns, including seasonal shifts and changes in commuting behavior.
Best-Fit Customer Segments for Pay-As-You-Go Model
- Low-mileage drivers
- Remote and hybrid workers
- Retirees
- Urban residents with limited driving frequency
- Multi-vehicle households where one vehicle is rarely used
This segment has grown post-pandemic as commuting patterns remain structurally lower in many metropolitan markets.
Strategic Value for Insurers
Mileage-based models serve multiple strategic purposes:
- Defensive positioning against direct-to-consumer Insurtech competitors
- Retention tool for low-usage policyholders who might otherwise shop aggressively
- Data-rich entry point into broader telematics insurance programs
- Brand alignment with fairness-based pricing narratives
According to industry studies, drivers consistently cite “paying for unused mileage” as a top dissatisfaction driver in auto insurance. Mileage-based pricing addresses that perception gap directly.
For carriers with strong analytics capability, this model can improve risk segmentation without fully transitioning to behavior-based scoring.
3. Pay How You Drive (Behavior-Based / Telematics Insurance)
Pay How You Drive is a form of telematics insurance where pricing is influenced not only by mileage, but by driving behavior. Data collected through mobile apps, plug-in devices, or embedded vehicle systems measures factors such as acceleration, braking, speed patterns, time of day, and in some programs, distraction indicators.
Unlike pure usage-based auto insurance models tied only to miles, this structure introduces behavior scoring into underwriting and pricing. Premium becomes partially dynamic, reflecting observed risk characteristics during the policy term.
Best-Fit Customer Segments for Pay How You Drive Model
- Younger drivers seeking discounts
- Safety-conscious households
- Parents monitoring teen drivers
- Digitally engaged policyholders
- Fleet-lite and gig drivers with trackable patterns
Behavior-based programs often attract customers who believe they are “better than average” drivers and want pricing that reflects that confidence.
Strategic Value for Insurers
Telematics insurance offers deeper strategic advantages than mileage-only models:
- Improved risk segmentation granularity
- More accurate frequency prediction models
- Early identification of deteriorating driving behavior
- Enhanced retention through engagement (driver score dashboards)
- Competitive differentiation in digital distribution
Industry research indicates that telematics-enabled policies can reduce claim frequency among participating drivers, particularly when feedback loops encourage safer driving behavior.
For insurers focused on underwriting accuracy rather than short-term pricing differentiation, this is a structural evolution. Behavioral data allows carriers to move beyond proxy variables and refine risk selection dynamically during the policy term. That can improve frequency forecasting, sharpen pricing adequacy, and reshape portfolio mix over time.
Related Read: Top 7 UBI Trends in the USA & How Auto Insurers Can Make the Shift
4. Subscription Auto Insurance
Subscription car insurance bundles auto coverage into a recurring monthly structure, often combined with vehicle access, maintenance, roadside assistance, or other mobility services. Instead of a fixed 6- or 12-month policy, coverage operates on a rolling subscription basis.
In some structures, insurance is embedded within a broader vehicle subscription. In others, the policy itself is structured as a month-to-month renewable agreement with simplified cancellation.
This model aligns insurance with subscription-based consumption patterns increasingly common across financial services and mobility ecosystems.
Best-Fit Customer Segments for Subscription Based Model
- Younger urban drivers
- Drivers using vehicle subscription platforms
- Customers seeking predictable monthly cost structures
- High-income convenience-focused consumers
- Households preferring bundled service models
This segment prioritizes simplicity and flexibility over long-term contractual commitment.
Strategic Value for Insurers
Subscription models create strategic opportunities beyond pricing:
- Integration into vehicle subscription ecosystems
- Increased customer engagement through bundled services
- Predictable recurring revenue flows
- Lower perceived commitment barriers at onboarding
- Potential cross-sell opportunities across mobility services
For carriers partnering with OEMs or mobility providers, subscription insurance becomes an embedded distribution play rather than a standalone product. The platform controls the purchase moment, bundles insurance into the monthly payment, and reduces shopping friction. That can improve conversion, but it also shifts economics around margin, data expectations, and channel leverage. In this setup, insurers win on underwriting performance, integration speed, and claims experience more than brand-led acquisition.
It also aligns with a broader shift toward recurring service relationships instead of fixed contracts. Customers increasingly expect one predictable monthly mobility bill, simple onboarding, and “change or cancel anytime” servicing. That raises the bar for billing accuracy, disclosure clarity, and near-real-time policy updates. Annual policy workflows often need modernization to deliver that experience consistently.
5. Embedded Auto Insurance
Embedded auto insurance is coverage offered seamlessly at the point of vehicle purchase, financing, or lease, often through OEMs, dealerships, digital marketplaces, or mobility platforms. Instead of the customer shopping separately, insurance is integrated directly into the purchase journey.
The coverage may be underwritten by a carrier but distributed through the partner’s digital ecosystem. In many cases, the insurance decision happens within minutes of vehicle selection.
Best-Fit Customer Segments for Embedded Auto Insurance
- Digital-first vehicle buyers
- Customers purchasing vehicles online
- First-time buyers seeking convenience
- OEM-loyal drivers
- Customers financing or leasing vehicles
Embedded models are particularly effective where the vehicle purchase journey is already digitized.
Strategic Value for Insurers
Embedded auto insurance transforms distribution economics.
Rather than competing in comparison marketplaces, insurers integrate upstream into the vehicle transaction itself. That reduces traditional shopping friction and can improve bind rates at a high-intent moment.
It also enables carriers to access structured vehicle data directly from the OEM or platform, improving underwriting inputs at bind.
However, embedded models shift power toward distribution partners. Margin compression, data ownership expectations, and platform dependency must be evaluated carefully.
6. On-Off Insurance (Toggle Activation Model)
On-Off insurance allows policyholders to activate or deactivate certain coverage components, typically collision or comprehensive, through a mobile app or digital portal. The core liability coverage often remains active to comply with state minimum requirements, while optional coverages can be toggled.
The concept is simple: pay only when the vehicle is actively being used. However, from a regulatory and underwriting standpoint, it is more complex than it appears.
This model is often positioned as a form of on demand auto insurance, but structurally it is closer to controlled exposure modulation within an active policy.
Best-Fit Customer Segments for On-Off Insurance
- Seasonal drivers
- Owners of secondary or recreational vehicles
- Urban residents who park vehicles long-term
- Remote workers with irregular driving patterns
- Cost-sensitive policyholders seeking flexibility
This model resonates with drivers who view inactivity periods as “unused premium.”
Strategic Value for Insurers
On-Off insurance can serve as a retention tool in rate-sensitive markets.
Instead of losing a customer due to premium pressure, carriers offer controlled coverage reduction during low-usage periods. This can preserve the relationship while protecting core liability exposure.
It also signals responsiveness to consumer expectations around flexibility. However, its financial benefit depends heavily on how frequently customers toggle and how exposure truly shifts. If poorly designed, it can create premium leakage without meaningful risk reduction.
Quick Comparison Matrix of Six On-Demand Auto Insurance Models
| Model | Best-Fit Segment | Primary Pricing Basis | Fraud / Adverse Selection Risk | Channel Fit | Operational Complexity |
|---|---|---|---|---|---|
| Pay As You Need (Time-Based) | Occasional drivers, borrowed vehicle users, short-term access | Duration-based (hour/day/week) | High at bind; event-driven activation risk | Strong D2C; niche insurtech; non-owner distribution | High – requires real-time rating, instant issuance, fraud scoring |
| Pay As You Go (Mileage-Based) | Low-mileage, remote workers, retirees | Verified miles driven | Moderate – mileage manipulation risk | D2C; retention tool for existing book | Moderate to High – dynamic billing, mileage validation, disclosure control |
| Pay How You Drive (Telematics Insurance) | Younger drivers, safety-focused households | Behavioral scoring + usage data | Algorithm scrutiny; data governance exposure | D2C; agent-assisted with digital overlay | High – telematics ingestion, scoring engines, compliance oversight |
| Subscription Car Insurance | Urban, mobility-platform users, convenience-focused customers | Recurring monthly pricing | Churn volatility; pricing adequacy risk | OEM partnerships; vehicle subscription ecosystems | Moderate – recurring billing, rolling renewals, cancellation logic |
| Embedded Auto Insurance | Digital vehicle buyers; OEM-loyal customers | Integrated real-time quote at POS | Channel concentration risk; disclosure scrutiny | OEM, dealer, marketplace integrations | High – API orchestration, instant bind, partner governance |
| On-Off Insurance | Seasonal or secondary vehicle owners | Toggle-based exposure modulation | Activation timing disputes; premium leakage | Primarily D2C mobile-first | High – real-time endorsements, audit trails, state compliance automation |
Risk and Compliance Considerations Before Launching Auto Insurance Product
On-demand auto insurance models introduce operational flexibility, but they also amplify compliance sensitivity. In the U.S., regulatory variation by state makes execution as important as product design.
Carriers evaluating temporary car insurance, usage-based auto insurance, telematics insurance, subscription car insurance, or embedded auto insurance must address several compliance dimensions early.
1. State Regulatory Variation
Auto insurance remains state-regulated.
Key considerations include:
- Minimum coverage duration requirements
- Financial responsibility laws
- Cancellation and non-renewal notice periods
- Filing requirements for telematics rating factors
- Restrictions on inducements in embedded sales models
Some states may limit how short a policy term can be. Others require explicit approval if telematics materially affects premium. Piloting in a limited number of aligned jurisdictions is often prudent before broader rollout.
2. Disclosure Clarity in Digital Journeys
On-demand structures are frequently sold through digital channels. That increases scrutiny around:
- Clear presentation of coverage limits
- Explanation of dynamic pricing components
- Toggle activation terms and conditions
- Renewal or subscription auto-renew logic
- Variable billing disclosures
Regulators increasingly evaluate whether consumers fully understand fluctuating premiums in mileage-based or telematics insurance programs. Ambiguity in digital UX can translate directly into complaint volume.
3. Proof of Insurance Timing
Real-time issuance creates compliance obligations.
Insurers must ensure:
- Instant generation of ID cards
- Timely reporting to state databases (where required)
- Clear timestamping of activation events (for On-Off models)
- Accurate lapse prevention controls
Coverage disputes around activation timing can quickly escalate into regulatory exposure if audit trails are weak.
4. Data Privacy and Telematics Governance
Behavior-based and mileage-based programs require careful data governance.
Considerations include:
- Customer consent protocols
- Data storage security
- Algorithm transparency
- State privacy laws (including emerging data protection statutes)
- Disparate impact analysis
Telematics data may be considered sensitive personal information depending on jurisdiction. Clear governance frameworks reduce both litigation and reputational risk.
5. Cooling-Off Periods and Refund Logic
Short-duration and subscription models raise questions about:
- Refund calculations
- Grace periods
- Mid-term premium adjustments
- Consumer rights in digital sales environments
States may require specific disclosures when coverage begins immediately at bind. Failure to align refund logic with state-specific rules can erode profitability and increase regulatory scrutiny.
Related Read: Questions Every Carrier Must Ask Before Launching a New Line of Business
Conclusion
On-demand auto insurance is not a replacement for the annual policy, it is a portfolio design decision. The opportunity is in choosing the right model for the right goal: time-based cover as an acquisition bridge, mileage-based and telematics insurance to sharpen segmentation, embedded and subscription models to expand distribution, and on-off structures to defend retention. Insurers win here by aligning underwriting discipline, channel strategy, and operational capability before scaling.
The practical path forward is targeted and deliberate: choose one segment, pilot in limited states, validate loss performance, and pressure-test compliance and servicing workflows. As insurers evaluate which model to build, and how to build it, strategic clarity becomes critical.
This is where insurance strategic consultants such as Practo Insura play a role, helping carriers assess distribution fit, risk appetite, and technology readiness before committing capital. In an environment where flexibility is becoming expected, the advantage will belong to insurers that design on-demand capabilities intentionally, not reactively.
How to Build Right Customer Experience Technology Stack for P&C Insurer in the USA
In today’s U.S. property & casualty (P&C) insurance landscape, customer expectations are rapidly evolving, and carriers that fail to modernize risk losing relevance.
Beyond expectations, strong customer experience (CX) delivers measurable business impact. A Forrester study found that companies prioritizing CX grow revenue at nearly twice the rate of competitors, underscoring how experience excellence directly ties to retention, loyalty, and lifetime value.
For U.S. P&C insurers, meeting these expectations isn’t just about convenience, it’s a competitive necessity. The modern policyholder wants digital simplicity, real-time updates, and seamless interactions across devices and channels, while independent agents increasingly demand tools that streamline quoting, servicing, and collaboration.
What Is Considered as CX Technology?
The CX tech stack is the set of digital platforms, tools, and connected technologies that enable an insurer to engage customers and agents effectively throughout their journey, from quote and bind, through service and claims, to renewal and advocacy.
This is not a single tool. A CX tech stack is a connected ecosystem that brings together engagement, service, data, and communication layers so every interaction feels consistent, responsive, and relevant. When done right, it reduces friction for customers, improves productivity for agents and service teams, and gives leadership better visibility into what’s actually happening across the customer journey.
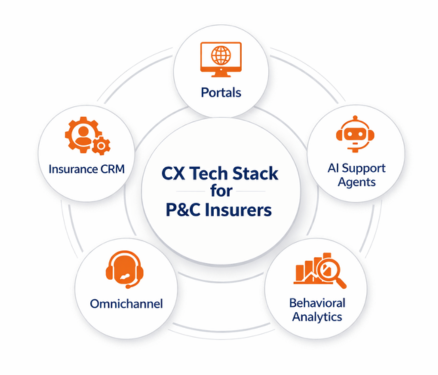
At a high level, a modern insurance CX stack typically includes five core pillars:
- Self-Service Portals: These are the digital front doors of the insurer. Portals allow users to get quotes, view policies, make payments, submit claims, upload documents, and track status without needing to call or email.
- Insurance-Specific CRM: A CRM tailored for insurance manages relationships, tracks interactions, and supports lifecycle workflows across sales, service, renewals, and claims, while understanding policies, endorsements, and accounts, not just "contacts".
- AI Support Agents: These include chatbots and voice bots designed to handle common questions, guide users through tasks, and assist service teams by automating repetitive interactions and triaging requests.
- Behavioral Analytics Tools: These systems analyze how customers and agents actually behave across digital touchpoints, what they click, where they drop off, and what drives conversions or frustration, so experiences can be continuously improved.
- Omnichannel Communications Layer: This ensures consistent, coordinated communication across email, SMS, chat, portals, call centers, and notifications, so customers don’t feel like they’re starting over every time they switch channels.
How to Build the Right CX Tech Stack
Building the right CX technology stack for a P&C insurer isn’t about buying the most tools, it’s about choosing the right capabilities that work together to support policyholders, agents, and internal teams across the full customer lifecycle. The goal is simple: reduce friction, increase transparency, and make every interaction feel easier and more relevant.
A strong CX stack should be designed around how insurance is actually sold, serviced, and supported in the U.S. market, across quoting, policy changes, billing, claims, renewals, and support.
1. How to Select Self-Service Portals
Self-service portals are the primary digital interface between an insurer and its users. They shape first impressions, daily interactions, and long-term satisfaction for both policyholders and distribution partners.
What Self-Service Portals Should Do
A modern insurance self-service portal should support:
- Policy Access and Document Management: Users should be able to view policies, endorsements, ID cards and download or upload documents without contacting support.
- Billing and Payments: The portal should allow users to view invoices, set up autopay, make one-time payments, and track payment history in real time.
- Claims Submission and Status Tracking: Customers should be able to file claims, upload photos or documents, and track claim progress without calling a service center.
- Endorsements and Policy Changes: Simple changes like address updates, vehicle changes, or coverage adjustments should be requestable digitally with clear status updates.
- Agent-Specific Workflows: Agent portals should support quoting, bind requests, renewals, and book-of-business views, not just basic policy lookups.
- Secure Messaging and Notifications: The portal should provide a secure way to communicate with the insurer and receive alerts about payments, claims, or required actions.
Why Self-service Portals are Foundational for CX
Self-service portals are often the most-used digital touchpoint in an insurer’s ecosystem. When they work well, they reduce call volumes, speed up service, and give customers a sense of control. When they don’t, frustration builds quickly and spills into call centers, agent relationships, and retention metrics. In practice, portals set the baseline for how “modern” and “easy to do business with” your company feels.
Selection Criteria for Self-service Portals
When evaluating self-service portals, focus on:
- User Experience and Accessibility: The interface should be simple, mobile-friendly, and usable by non-technical customers and agents without training.
- Insurance Workflow Coverage: The portal must support real insurance use cases, policies, endorsements, billing, and claims, not just generic account management.
- Integration with Core Systems: It should connect cleanly to your PAS, billing, and claims systems so users see accurate, real-time information.
- Security and Compliance: Look for strong identity management, role-based access, audit trails, and compliance with U.S. data protection and insurance regulations.
- Configurability and Branding: The platform should allow you to tailor journeys, forms, and content without heavy custom development.
- Scalability and Performance: The portal must handle peak loads during events like weather catastrophes, renewal cycles, or billing runs without degrading the experience.
Related Read: Do You Need an Insured Portal or Agent Portal First?
2. How to Select an Insurance-Specific CRM
An insurance-specific CRM is the system of record for relationships, interactions, and service journeys across sales, service, underwriting, and renewals. Unlike generic CRMs, it must understand policies, accounts, risks, and distribution models unique to P&C insurance.
What an Insurance CRM Should Do
A CRM built for insurance should support:
- Unified Customer and Account View: It should bring together policies, claims, billing status, interactions, and documents into a single, coherent view for service and sales teams.
- Lifecycle and Renewal Management: The system should track customers from quotes to bind to renewal, including reminders, follow-ups, and renewal workflows tied to policy terms.
- Agent and Broker Relationship Management: For carriers and MGAs, the CRM should manage agencies, producers, appointments, commissions, context, and performance metrics, not just end customers.
- Interaction and Case Management: Every call, email, chat, or task should be logged and traceable, with service cases routed and prioritized based on insurance-specific rules.
- Sales and Service Workflow Automation: The CRM should automate tasks like follow-ups, document requests, underwriting handoffs, and service escalations to reduce manual work.
- Integration with Core Insurance Systems: It should synchronize with PAS, claims, and billing systems so teams always work with current, authoritative data.
Why Get an Insurance-specific CRM
In P&C insurance, customer experience is shaped by continuity and context. An insurance-specific CRM ensures that every team member sees the same history, understands the policy context, and can respond without asking customers to repeat themselves. This improves service speed, reduces errors, and creates a more consistent experience across sales, service, and claims.
Key Requirements to Check in Insurance CRM
When selecting an insurance CRM, prioritize:
- Insurance Data Model Fit: The CRM must natively support policies, accounts, risks, and relationships, not force these into generic “contact” and “deal” structures.
- Workflow Flexibility: Look for configurable workflows that match underwriting, servicing, and renewal processes without heavy custom code.
- Integration Architecture: The platform should offer strong APIs and prebuilt connectors to PAS, claims, billing, and portal systems.
- Usability for Frontline Teams: Service reps, agents, and sales teams should be able to use it efficiently without complex training or workarounds.
- Reporting and Visibility: The CRM should provide clear views into pipeline, service backlogs, renewal risks, and customer activity across channels.
- Scalability and Governance: It must support growth across lines of business, states, and distribution models while maintaining data quality and access controls.
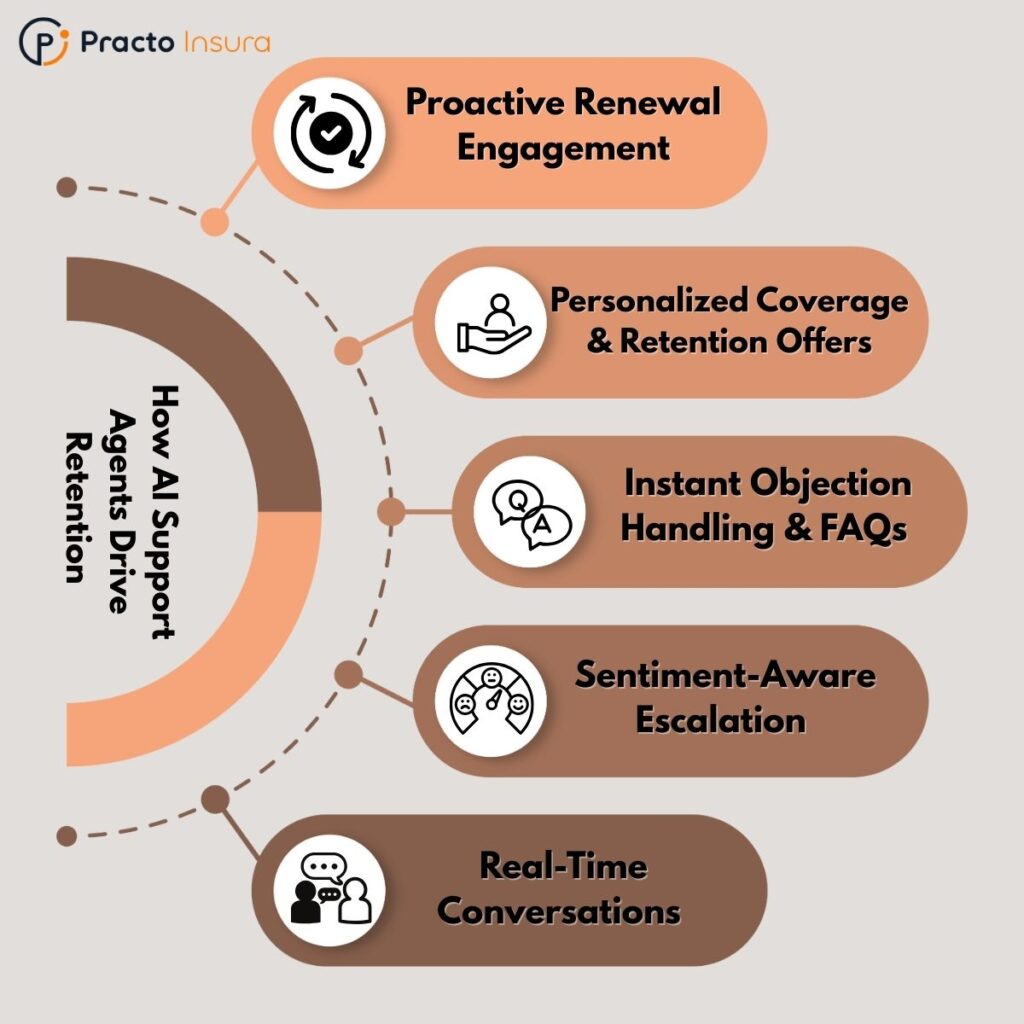
3. How to Select AI-powered Support Agents
AI-powered support agents are becoming a frontline layer of customer interaction in modern P&C insurance. When implemented correctly, they handle routine requests, guide users through processes, and support service teams, without replacing the human touch where it matters.
What AI Support Agents Should Do
In an insurance context, AI virtual assistants should support:
- Answer Common Policy and Billing Questions: They should handle FAQs like coverage details, payment status, due dates, and policy documents using real-time data from core systems.
- Guide Users Through Transactions: Assistants should walk customers through actions such as filing a claim, requesting an endorsement, or updating personal information step by step.
- Triage and Route Requests: The system should classify inquiries and route complex cases to the right human team with proper context and history attached.
- Support Both Customers and Agents: AI assistants should serve policyholders externally and help agents or CSRs internally find information, forms, or process guidance faster.
- Operate Across Channels: They should work consistently across web chat, mobile apps, portals, and even voice channels, not just a single interface.
- Learn from Interactions: Over time, the assistant should improve accuracy and coverage based on real user behavior, feedback, and new content.
Why AI Agents Are Important
For insurers, AI assistants reduce wait times, lower call center volume, and provide 24/7 support without linear increases in staffing. More importantly, they create faster, more predictable experiences for customers and agents, while freeing human teams to focus on complex, high-value interactions.
Related Read: How AI Support Agents Help Insurers Improve Retention at Renewal Time
Checklist to Select AI Support Agents
When evaluating AI virtual assistants, focus on:
- Insurance Domain Understanding: The platform should handle insurance terminology, workflows, and scenarios, not just generic Q&A.
- Integration with Core and CX Systems: It must connect to PAS, claims, billing, CRM, and portals to deliver accurate, real-time responses.
- Conversation Design and Control: Look for tools that allow you to design, test, and govern conversation flows rather than relying only on black-box AI behavior.
- Human Handoff Capabilities: The assistant should smoothly transfer conversations to live agents with full context when automation reaches its limits.
- Security and Compliance: Ensure strong data handling, audit trails, and controls appropriate for regulated insurance environments.
- Analytics and Continuous Improvement: The platform should provide insight into deflection rates, resolution times, failure points, and content gaps.
Related Read: Voice vs. Chat AI Virtual Agent in Insurance Support: Do You Need Both?
4. How to Select a Behavioral Analytics Tool
Behavioral analytics tools help insurers understand what customers and agents actually do across digital touchpoints, not just what they say. This layer turns usage data into actionable insight for improving journeys, reducing friction, and increasing conversion and retention.
What Behavioral Analytics Tool Should Do
A behavioral analytics tool for a P&C insurer should support:
- Track User Journeys Across Channels: It should follow how users move through portals, apps, and web experiences, showing common paths, drop-offs, and loops.
- Identify Friction and Abandonment Points: The system should highlight where users struggle, such as incomplete quotes, stalled claims submissions, or failed payments.
- Segment Users by Behavior: It should group users based on actions (not just demographics), such as “frequent self-service users", “claim-heavy users", or “renewal-risk users".
- Measure Feature and Content Usage: Teams should be able to see which features are actually used, which are ignored, and which cause confusion or delays.
- Support Experimentation and Optimization: The tool should enable A/B testing or experience comparisons to validate changes to forms, flows, and messaging.
- Link Behavior to Outcomes: It should connect digital behavior to business results like quote conversion, claim cycle time, call deflection, or renewal rates.
Why Behavioral Analytics Tool Is Important
Without behavioral analytics, insurers are forced to rely on assumptions, anecdotes, or lagging indicators. Behavioral insight makes CX measurable and improvable. It allows teams to fix the right problems, prioritize the right investments, and continuously refine digital experiences based on real usage, not opinions.
Selection Criteria for Behavioral Analytics Tool
When choosing a behavioral analytics platform, prioritize:
- Cross-Platform Data Coverage: It should work across web, mobile, and portal experiences to provide a complete journey view.
- Privacy and Compliance Controls: The tool must support data masking, consent management, and compliance with U.S. data and insurance regulations.
- Actionable Visualization and Reporting: Insights should be easy for product, CX, and operations teams to understand and act on, not just data dumps.
- Integration with CX and Core Systems: The platform should connect with CRM, portals, and support tools to tie behavior to customers and outcomes.
- Scalability and Performance: It must handle high volumes of events during peak periods like storms, renewals, or billing cycles without data loss.
6. Omnichannel Communications Layer
The omnichannel communications layer is what ensures customers and agents experience your insurer as one coherent company, not a collection of disconnected departments and tools. It coordinates how messages are sent, received, and continued across every channel.
Why It Matters in CX
In insurance, conversations rarely happen in a single session or channel. A customer might start with a portal, receive an email, follow up by phone, and continue via chat. Without an omnichannel layer, these interactions become fragmented, forcing users to repeat themselves and creating inconsistent responses. A strong omnichannel foundation ensures continuity, context, and consistency, which are core drivers of trust, satisfaction, and perceived service quality.
Communications Layer Requirements
An effective omnichannel communications layer should provide:
- Channel Orchestration: The ability to coordinate conversations across email, SMS, chat, portals, and call centers so interactions feel continuous, not reset.
- Unified Conversation History: All interactions should be logged and visible to service teams and systems, regardless of where they started.
- Event-Driven Notifications: The system should trigger timely messages for events like payment reminders, claim status updates, document requests, or renewal notices.
- Personalization and Context Awareness: Messages should reflect the customer’s policy, claim, or account situation, not generic templates.
- Integration with CX and Core Systems: It must connect to CRM, portals, claims, and billing systems to ensure accurate, relevant communication.
- Governance and Compliance Controls: The platform should support consent management, message audit trails, delivery tracking, and regulatory record-keeping.
10 Common Mistakes to Avoid When Building a P&C CX Tech Stack
- Selecting tools without a clear integration plan: If portals, CRM, claims, billing, and communications cannot share context reliably, customers receive inconsistent answers and teams rework the same requests.
- Treating portals as a design exercise instead of a servicing platform: A polished interface is meaningless if users can’t complete core actions like endorsements, FNOL, document uploads, payment actions, and status tracking end-to-end.
- Overlooking agent workflows and distribution usability: Weak agent servicing (quoting speed, renewal support, book-of-business visibility) creates friction in the channel that drives the majority of P&C growth.
- Implementing a generic CRM that lacks an insurance-native data model: When policy, risk, household, vehicle/property, claim, and producer relationships are forced into generic objects, workflow breaks, reporting becomes unreliable, and adoption drops.
- Deploying AI assistants without transactional capability: If the assistant only answers FAQs and cannot access real-time policy/claim/billing context or guide users through tasks, it will not reduce volume or improve experience.
- Failing to design a controlled human handoff for AI interactions: Handoffs must transfer intent, conversation history, and relevant policy or claim context; otherwise customers repeat themselves and service confidence declines.
- Measuring digital activity but not linking it to business outcomes: Event tracking without outcome mapping (quote completion, claim cycle time, payment success, renewal retention) produces dashboards, not decisions.
- Underestimating data privacy, consent, and governance requirements: Behavioral analytics and communications must include masking, consent controls, retention rules, and auditability to avoid regulatory and reputational risk.
- Building “multi-channel” instead of true omnichannel continuity: Multiple channels are not enough. Customers should be able to move between portal, email, SMS, phone, and chat without losing context or restarting the process.
- Not preparing for surge conditions and operational resilience: CAT events, renewal waves, and billing cycles expose weaknesses. If performance, routing, and messaging fail under load, CX damage is immediate and measurable.
Conclusion
For U.S. P&C insurers, CX is defined by how easily policyholders and agents can quote, service policies, pay bills, file claims, and get answers. The right CX tech stack connects portals, CRM, AI assistants, analytics, and omnichannel communications into one consistent journey. When these layers work together, service becomes faster, clearer, and more predictable. That’s when CX turns into a real operating advantage.
Most CX programs fail due to execution gaps: disconnected tools, generic platforms that don’t fit insurance workflows, and automation that can’t complete real transactions. Without integration and governance, customers repeat information, updates get missed, and call volume rises
The goal is resilience and scale, especially during renewals and CAT-driven volume spikes. Platforms like Practo Insura support this model with CX tools such as an insured portal and AI support agents designed for P&C insurance support. This helps carriers and MGAs move from fragmented touchpoints to a connected experience layer. Over time, consistency becomes the differentiator customers and agents remember.
How to Build Right Compliance Technology Stack for P&C Insurer in the USA
Insurance leaders often ask: “Why are our filings taking so long?” or “Why are we still getting objections even after internal sign-off?” The answer usually isn’t the regulators, it’s the compliance architecture beneath your systems.
In 2023, U.S. regulators increased penalties on financial firms by 69%, underscoring growing scrutiny around how well companies enforce and demonstrate compliance across the board.
For P&C insurers, the compliance technology stack is the architecture that connects your regulatory brain with your operational body. It's more than just tracking rules or filing rates; it’s the ecosystem that ensures every action your systems take, from quoting to cancellation, aligns with legal requirements, audit readiness, and internal governance standards.
More than a safeguard, this stack is the foundation layer that supports faster launches, cleaner filings, and stronger CX, without increasing risk exposure.
What Is Considered Compliance Tech in Insurance?
The term “compliance technology” in insurance often gets oversimplified, reduced to rule tracking or filing software. In reality, compliance tech is a multi-layered operational framework designed to embed regulatory, legal, and audit-readiness into the daily systems of a P&C insurer.
Think of it not as a single tool, but as a stack of interoperable components, each responsible for a different phase of the compliance lifecycle. These tools enable insurers to handle ever-changing DOI rules, justify filings, validate rule logic, record approvals, and retain defensible evidence.
The 6 Key Layers of the Compliance Stack
Here’s a quick preview of what makes up a modern compliance tech stack:
- Rules & Forms Repository: Centralized storage of regulatory rules, state form templates, and product configurations.
- Filing Workflow System (SERFF Ops Enablement): Manages end-to-end filing lifecycle across states, including objections, approvals, and DOI correspondence.
- Controls & Approval Workflows (Governance Layer): Enforces internal sign-offs, policy governance, exception handling, and access controls.
- Compliance Testing & Pre-Filing Validation: Simulates real-world scenarios to catch compliance issues before filings or releases.
- Audit Records & Retention Layer: Captures immutable logs of filings, decisions, exceptions, and document revisions for audit and legal use.
- Compliance Integration Layer: Connects the stack to PAS, rating engines, claims, and CX layers through APIs and events.
Each of these components plays a different but interdependent role. Together, they turn compliance from a reactive function into a proactive, automated, and scalable advantage.
Related Read: How to Build Right Core Technology Stack for P&C Insurer in the USA
How to Build Right Compliance Tech Stack
1. How to Select the Regulatory Rules & Forms Repository
Every compliance stack starts here. The rules and forms repository is the system of record for all regulatory content, holding the latest rules, filing templates, coverage mandates, and product configurations across states.
What a Rules/Forms Repository Does
A strong repository should offer:
- Centralized Rule Storage: Houses all DOI regulations, form templates, and product rules in one secure, searchable location.
- State-Specific Versioning: Maintains version control across jurisdictions so teams can track what applies where and when.
- Change Detection & Alerts: Flags updated mandates, withdrawn forms, or regulatory changes to prevent non-compliant filings.
- Integration with Rating & Filing Systems: Enables seamless flow of approved rules and forms into your rating engine and SERFF interface.
- Role-Based Access & Governance: Restricts edits, approvals, and publishing rights to designated compliance owners or teams.
- Traceable History: Keeps a defensible log of who changed what, when, and why, essential for audits or DOI inquiries.
Why It’s Foundational for Compliance
This layer is where compliance starts and errors propagate. If outdated rules are pulled into filings, forms, or policy documents, it leads to objections, rework, or worse, regulatory action. A real-time, governed repository ensures accuracy at the source and reduces risk across the stack.
Checklist for Selecting a Rules Repository System
Choose a repository that meets these key requirements:
- Architecture: Should support cloud-native or hybrid deployments with high uptime and backup resilience.
- Functional: Must include searchability, tagging, rule/form relationships, and workflow assignment features.
- Data: Needs structured metadata (e.g., effective dates, jurisdictions, product lines) for filtering and reporting.
- Operational: Should offer automation for rule updates and integrate easily into policy and filing workflows.
- Compliance: Must maintain full audit trails, role-based access, and immutable storage for versioning integrity.
2. How to Select a Filing Workflow System (SERFF Ops Enablement)
Once rules and forms are ready, insurers need a system to coordinate, submit, and track regulatory filings, especially across multiple states. The filing workflow system acts as the execution engine of your compliance stack.
What a Filing Workflow System Does
Core functionalities include:
- Filing Lifecycle Management: Orchestrates end-to-end filing steps, from draft to submission to approval.
- SERFF Integration: Direct interface with the NAIC (National Association of Insurance Commissioners) SERFF system to push/pull filings and responses without manual uploads.
- Objection Handling Workflow: Manages back-and-forth communication with DOI teams and tracks version changes tied to objections.
- Collaboration & Task Assignment: Enables teams (product, actuarial, legal) to coordinate inputs, approvals, and file-ready documents.
- Submission Evidence Storage: Stores copies of filings, timestamps, approval letters, and regulator correspondence for audit purposes.
- Multi-State Variation Handling: Supports branching logic for state-specific filing differences while keeping the core structure unified.
Why Filing Workflow Matters
Without it, teams fall into email- and spreadsheet-driven chaos, increasing the risk of missed deadlines, inconsistent filings, or lost regulator trust. A modern workflow system centralizes control and helps insurers manage scale without losing compliance precision.
Key Requirements for Filing Workflow
Choose a system that supports:
- Workflow: Should model end-to-end filing processes with configurable steps, task queues, and filing types.
- Collaboration: Must support multi-user access, role-based tasks, and comment tracking across departments.
- Evidence: Needs automated retention of submission files, approvals, and regulatory responses with time-stamped logs.
- Reporting: Offers dashboards for upcoming deadlines, approval status, objection trends, and submission SLAs.
3 How to Select Controls & Approval Workflows (Governance Layer)
Governance is what separates structured compliance from impulsive decision-making. This layer enforces internal accountability, ensures regulatory sign-offs are auditable, and prevents unauthorized changes from creeping into filings or production systems.
With strong controls in place, insurers can prove due diligence, reduce regulatory pushback, and avoid internal disputes over approvals.
What Controls/Approvals Should Govern
A proper governance layer should:
- Enforce Review Chains: Define required sign-offs (e.g., compliance, legal, actuarial) before filing or product changes go live.
- Support Multi-Step Approvals: Allow parallel or sequential approvals for state filings, pricing updates, or rating changes.
- Track Exceptions and Overrides: Document when rules were bypassed and why, creating defensible logs for audit or legal teams.
- Limit Access Based on Role: Prevent unauthorized users from publishing, editing, or pushing changes into production.
- Log Every Action: Capture who approved what, when, and under what conditions, with time stamps and justifications.
- Prevent “Shadow Edits”: Block untracked changes by routing all updates through governed workflows.
Why Controls Are a Compliance Multiplier
Compliance isn’t just about what’s in the system, it’s about who touched it and how. Without controlled workflows, even the best tech stack is vulnerable to human error, internal risk, and audit failures. Governance multiplies the effectiveness of every other compliance layer by enforcing discipline and transparency.
What to Look for in a Governance Layer
Look for systems that excel in:
- Security: Role-based access control, approval hierarchies, and protection against unauthorized edits.
- Evidence: Maintains a full audit trail of decisions, approvers, timestamps, and comments.
- Exceptions: Tracks rule deviations with required explanations and links to risk owners.
- Integration: Should plug into filing, PAS, and change management systems so governance is enforced at every step.
4. How to Select a Compliance Testing & Pre-Filing Validation Layer
Before you submit a filing or push a product live, there’s one last crucial gate: testing. This layer simulates regulatory scenarios, runs validations against known rules, and detects logic gaps or potential objections before the DOI or an auditor does.
What It Tests
An effective testing and validation layer should include:
- Regulatory Rule Alignment: Verifies that all configured rules match current state and DOI requirements.
- Rate & Rule Consistency: Flags inconsistencies between product rates, underwriting rules, and forms.
- Objection Pattern Simulation: Tests filings against historical DOI objections to preemptively correct problem areas.
- Scenario Testing: Runs hypothetical policy scenarios to validate outputs and edge cases.
- Pre-Filing Validation Reports: Generates summaries of issues, warnings, and clean records with timestamps for audit use.
- Automated Regression Checks: Ensures changes don’t accidentally violate older approvals or product constraints.
Why Testing Is Critical
A single missed objection pattern or misaligned rating rule can trigger multi-week DOI delays, damage regulator trust, or stall launches. Testing ensures that what you file is not only accurate, but defensible, minimizing costly back-and-forth cycles.
Must-Haves in a Compliance Testing Platforms
Look for a platform that provides:
- Scenario Coverage: Supports wide-ranging test inputs, custom scenarios, and jurisdictional logic.
- Automation: Enables scheduled runs, rule validations, and impact analysis without manual work.
- Reporting: Delivers clear, exportable validation reports with logs, issue types, and user actions.
5. How to Select Audit Trail & Retention Layer
When regulators, auditors, or legal teams ask, “who changed what and why?”, you need more than just answers, you need evidence. This layer is responsible for capturing, retaining, and linking every action tied to filings, rules, approvals, and exceptions.
It ensures that your compliance posture isn’t just strong, it’s provable under scrutiny.
What This Layer Captures
An effective audit record system should track:
- Filing Artifacts: Every submitted form, rate manual, DOI correspondence, and approval letter.
- Approval History: Who signed off, in what sequence, with what rationale and timestamps.
- Change Logs: Edits to rules, filings, templates, or rate structures with before/after comparisons.
- Exception Documentation: Justifications for overridden workflows or skipped steps, linked to risk owners.
- Retention Timelines: Archived data based on regulatory hold periods (e.g., 7+ years) and internal policies.
- Linkages Across Systems: Traceability from PAS or claims back to the original rule, form, or filing decision.
Why It’s Essential
Audits don’t happen on your timeline, and neither do legal disputes. Without secure, traceable retention, insurers face reputational risk, operational delays, and even penalties for being unable to prove past decisions. This layer turns reactive scramble into readiness on demand.
What to Check in an Audit Records System
Prioritize platforms that support:
- Immutability: Stored records should be tamper-proof and write-once, with cryptographic or version control safeguards.
- Legal Hold: Enables preservation of specific records under legal investigation or compliance audit.
- Retrieval: Fast, indexed access to records by date, product, jurisdiction, or filing ID.
- Linkage: Connects audit records to workflows, approvals, filings, and system-of-record references.
6. How to Select a Compliance Integration Layer
Even the best compliance systems fail if they operate in isolation. Without integration, you’re relying on manual handoffs, inconsistent logic, and duplicate entries, all of which increase risk. A well-integrated layer ensures:
- Regulatory rules are enforced at the point of quote or bind
- Changes flow downstream to CX and billing systems
- Exceptions and approvals are visible across teams
- Compliance doesn’t slow you down, it runs alongside operations
It’s how compliance becomes a real-time capability, not just a filing checkpoint.
Requirements for a Modern Integration Layer
Key technical and operational features include:
- APIs: Expose rule data, approval status, and filing outputs to PAS, rating, and portals in real time.
- Event-Driven Architecture: Triggers compliance checks or workflows when specific actions occur (e.g., a new product release, rate change, or DOI update).
- Orchestration Capabilities: Coordinates data movement and process steps across tools (e.g., repository → workflow → filing → audit).
- Observability: Provides monitoring, logging, and alerts for integration failures, data mismatches, or process delays.
10 Common Mistakes to Avoid When Building Your Compliance Tech Stack
- Treating Compliance as a Project, Not a System: One-off fixes won’t scale, compliance needs to be built as a living system that evolves with regulations and business goals.
- Relying on Spreadsheets for Rule Management: Manual tracking leads to outdated versions, missed changes, and zero audit trails, especially in multi-state operations.
- Submitting Filings Without Pre-Validation: Skipping objection simulations or rule alignment checks often results in unnecessary DOI pushback and delayed approvals.
- Lack of SERFF Integration in Workflow Tools: Teams waste hours manually uploading, tracking, and updating filings when this could be automated and version controlled.
- No Governance Over Who Approves What: Without approval chains and role-based restrictions, unauthorized edits or skipped reviews can go unnoticed until audit time.
- Ignoring Exception Handling in Workflow Design: Systems that don’t document or route exceptions create blind spots, leading to future compliance or legal risks.
- Poor Retention Planning for Audit Records: Failing to implement immutability or legal hold policies means evidence could be overwritten, lost, or legally inadmissible.
- Siloed Systems Without API Connectivity: If rules aren’t embedded into PAS, rating, or claims systems, teams revert to manual workarounds, introducing inconsistency.
- No Central Source of Truth for Rules & Forms: Having multiple rule versions across teams (legal, actuarial, ops) leads to contradictory filings and compliance errors.
- Lack of Observability Across the Stack: Without integration monitoring, teams only find issues after a failed submission or customer complaint, reactive vs proactive.
Conclusion
A well-built compliance tech stack isn’t just about checking regulatory boxes, it’s the foundation that enables faster product launches, smoother filings, and confident audits. When each layer, from rules repository to audit retention, is connected and governed, compliance becomes a real-time capability, not a reactive burden.
Most insurers still rely on disconnected systems, manual handoffs, or outdated tools. These gaps create delays, objections, and risk exposure that scale with every state and product line.
Legacy tools and manual workarounds can’t keep up with modern compliance demands. Carriers need systems that validate, track, and prove compliance, as part of how they operate, not after the fact.
Practo Insura partners with insurers to rethink that foundation. As insurance strategic consultant, we help teams build flexible compliance stacks that support faster approvals, cleaner filings, and long-term regulatory confidence.
How to Build Right Core Technology Stack for P&C Insurer in the USA
U.S. P&C insurers are spending more on technology than ever before, and yet, many carriers still struggle with legacy systems that slow product launches, create compliance risks, and frustrate policyholders. That’s because modern insurance performance doesn’t start with customer experience; it starts with core technology.
Your core tech stack is the foundation of your operating model. It powers how policies are issued, claims are settled, billing is processed, and data is analyzed. Without a modern stack, even the best front-end portals or CX tools can’t deliver speed, accuracy, or compliance at scale.
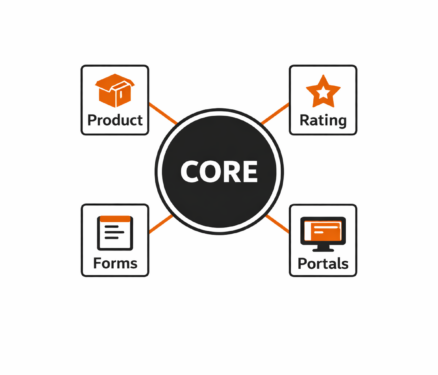
What Is Considered as Core Tech?
In the context of a modern U.S. P&C insurer, your core technology stack isn’t about flashy AI or digital front ends, it’s about the mission-critical systems that underpin your insurance operations. These are the technologies that directly support quoting, binding, servicing, billing, claims handling, and regulatory compliance
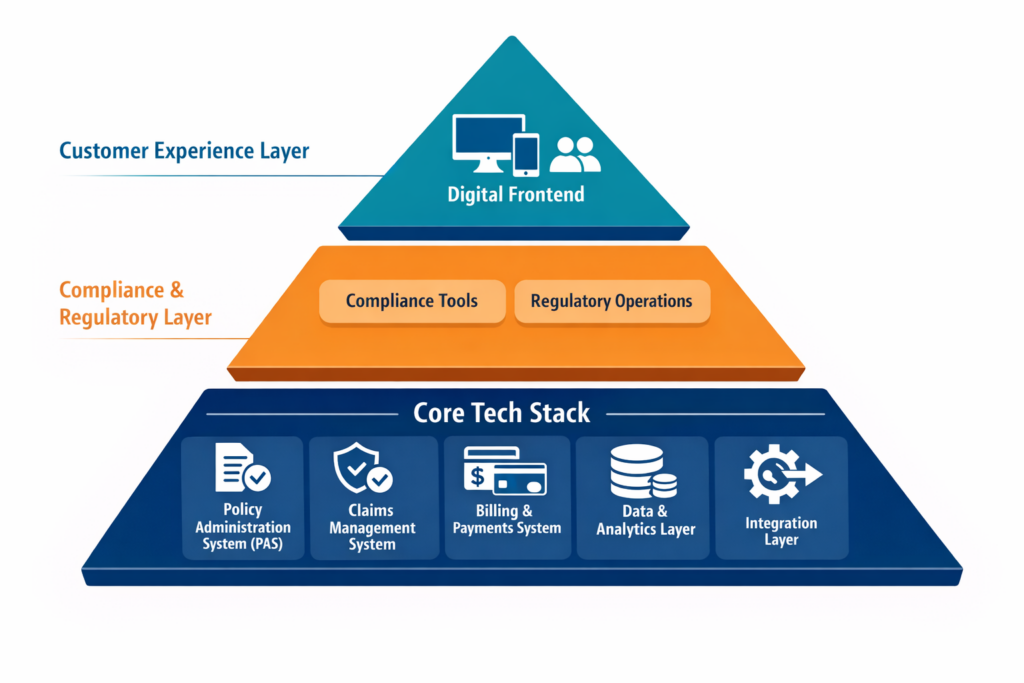
Core tech sits below your customer experience (CX) and compliance layers. It’s what keeps the business running before a chatbot responds, an agent logs in, and a filing is submitted to a DOI.
Here are the five components that make up the core stack:
- Policy Administration System (PAS): The operational core of insurance. It manages product definitions, ratings, quoting, issuance, endorsements, renewals, and cancellations. Think of it as your “product engine”.
- Claims Management System: Handles first notice of loss (FNOL), adjudication, approvals, and payouts. It’s critical for customer trust and operational cost control.
- Billing & Payments System: Manages invoicing, collections, commissions, refunds, and digital payment integrations. A key driver of both cash flow and customer satisfaction.
- Data & Analytics Layer: Serves as the backbone for reporting, pricing, actuarial work, operational dashboards, and regulatory analytics. Without this, insights stay siloed.
- Integration Layer: Serves as a connective tissue. It enables these systems to work together through APIs, event triggers, and shared workflows. It also links your core stack with CRM, portals, regulatory systems, and AI tools.
Together, these systems form the foundation of scalability. When chosen and configured properly, they allow for faster product launches, better compliance, and more automated servicing.
How to Select Right Core Technologies?
1. How to Select the Right Policy Administration System (PAS)
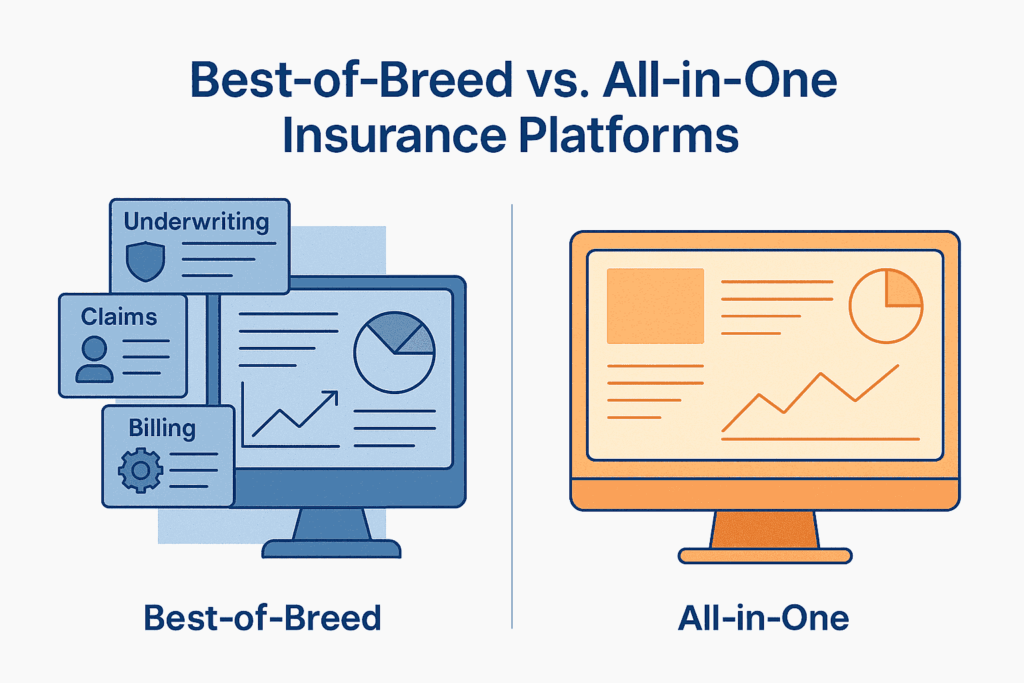
A modern Policy Administration System is the core of your insurance product engine. Everything else, claims, billing, portals, and compliance, ultimately relies on the data and structure the PAS provides.
What Functionalities Should a PAS Cover?
A robust PAS should support these key functionalities:
- Product Configuration & Rating: Define insurance products, coverage types, rating rules, and eligibility logic with minimal code.
- Quoting & Underwriting Workflows: Automate quote generation, risk assessment, and referral logic for speed and consistency.
- Policy Issuance & Document Generation: Seamless generation of bindable policies, notices, endorsements, and forms.
- Mid-Term Endorsements & Renewals: Support for lifecycle servicing without disrupting compliance tracking.
- Multi-State Compliance Support: Ability to adapt to jurisdictional differences in forms, rates, and rules.
- Version Control & Audit Trails: Full traceability across policy lifecycle changes to meet DOI and internal governance needs.
Why PAS Is Foundational?
Your PAS doesn’t just handle policies, it defines how your insurance products behave across every channel and process. It’s the single source of truth for coverage logic, rate application, compliance enforcement, and downstream data. A weak PAS leads to quoting errors, compliance gaps, and slower market entry. A strong PAS sets the rhythm for your entire operation.
Key Evaluation Criteria When Selecting a PAS
When evaluating a PAS, insurers should assess:
- Architecture Requirements: Cloud-native, API-first, modular design that supports scalability, containerization, and version upgrades with low downtime.
- Functional Coverage: Out-of-the-box support for personal/commercial lines, ISO integration, rate/test environments, and full policy lifecycle servicing.
- Data Capabilities: Structured data model, event-driven updates, and support for data lineage, essential for analytics, filings, and claims triggers.
- Operational Fit: Role-based access, workflow configurability, task queues, and bulk operations that align with underwriting and servicing models.
- Compliance Enablement: Jurisdiction-aware rule logic, filing documentation exports, and audit-ready logs help streamline SERFF filings and DOI inquiries.
2. How to Select a Claims Management System?
While the PAS governs the structure of insurance products, the claims system plays a critical role in fulfilling the insurer’s contractual obligations. It’s the part of your operation that directly affects the customer’s experience, how quickly, fairly, and smoothly a claim is handled.
What Functionalities Should a Claims Management System Cover?
A modern claims platform should support:
- First Notice of Loss (FNOL) Intake: Multi-channel FNOL capture (web, phone, email, mobile app) with structured triage logic.
- Automated Adjudication Rules: Configurable rules engine for routing, approvals, and fraud detection without constant IT involvement.
- Adjuster Workflows & Case Management: Assign tasks, manage caseloads, track SLAs, and escalate exceptions with full visibility.
- Vendor Integration & Payment Processing: Support for third-party services like repair shops, loss assessors, or medical networks, with seamless disbursements.
- Communications & Document Management: Templates, correspondence logs, e-signatures, and claim package automation for clear stakeholder communication.
- Reserving & Recovery Management: Built-in support for financial reserving, subrogation, and salvage to ensure accurate loss ratios and recoverables.
Why Claims Management System Matters in Core?
Claims isn’t just about payouts, it’s about delivering on the policy promise. Poor claims systems create operational delays, leakage, and litigation risks. A well-designed claims platform builds trust, improves outcomes, and reduces cost per claim, all while feeding valuable data back into underwriting and actuarial models.
Key Evaluation Criteria When Selecting a Claims System
When selecting a claims management system, insurers should evaluate:
- Architecture Requirements: API-first with workflow engines, event triggers, and flexible deployment (cloud, hybrid, or on-prem) for future-proof scalability.
- Functional Coverage: End-to-end support for FNOL to closure across multiple LOBs, including property, auto, liability, and specialty.
- Efficiency & Automation: Low-code workflows, straight-through processing (STP) without manual intervention, automatic adjudication based on coverage and thresholds, and proactive fraud flagging.
- Data Management: Real-time reporting dashboards, loss ratio visibility, integration with PAS for coverage validation, and audit logs for compliance.
3. How to Select a Billing & Payments System?
Billing isn’t just about collecting premiums, it’s a major touchpoint in the policyholder journey. Your system needs to support flexible plans, multiple payment channels, agent commissions, and clear financial reconciliation.
What Should a Billing System Cover?
Key capabilities of a modern insurance billing system include:
- Invoicing & Statement Generation: Automates invoice schedules, reminders, and dunning letters based on billing plans and premium frequency.
- Payment Processing: Accepts multiple methods, ACH (Automated Clearing House), credit/debit cards, digital wallets, and supports integrations with processors and gateways.
- Commission Handling: Tracks agent/broker commissions, overrides, and adjustments with full audit visibility.
- Installment & Recurring Plans: Enables flexible billing frequencies (monthly, quarterly, annual) and supports mid-term changes.
- Refunds, Cancellations & NSFs: Automates processing of refunds, cancellations for non-payment, and handling of bounced or declined payments.
- Reconciliation & Financial Reporting: Connects to general ledger systems and provides real-time dashboards for receivables, cash application, and audits.
Why Billing System Is Core?
Billing and payments touch every insured, every policy, every month. The system must balance financial accuracy, operational efficiency, and user experience. A strong billing engine also ensures compliance with premium collection laws, state cancellation rules, and finance charges, while giving insureds the payment flexibility they expect.
Checklist to Select Right Billing Technology
When evaluating billing systems, insurers should assess:
- Architecture Requirements: Look for modular, cloud-native systems with support for secure payment integrations, PCI compliance, and containerized services.
- Functional Fit: Ensure the system can handle both direct and agency billing, billing plan variations, commission hierarchies, and real-time payment updates.
- Payment Capabilities: Support for autopay, third-party payments, refunds, and split payments, with tokenized card storage and fraud monitoring.
- Finance & Compliance Readiness: Built-in reconciliation tools, state-specific cancellation logic, notice templates, and financial audit trails to meet statutory and GAAP requirements.
4. How to Select the Data & Analytics Layer?
A modern insurer can’t operate effectively without a strong data foundation. The data layer powers everything from pricing and claims trends to regulatory reporting and AI models. Without it, teams are stuck with siloed reports, outdated spreadsheets, and blind spots across operations.
What Should a Data Layer Cover
The data & analytics layer should enable:
- Enterprise Data Consolidation: Brings together structured and unstructured data from PAS, claims, billing, CRM, and third-party systems into a central repository or lake.
- Operational Dashboards & Reporting: Provides role-specific dashboards for underwriting, claims, finance, and compliance, updated in real time.
- Regulatory & Compliance Analytics: Enables timely filings, DOI responses, and internal audits with traceable, structured data.
- Predictive Modeling & Actuarial Insights: Supports pricing, reserving, and risk modeling with access to clean, reliable historical and real-time data.
- Embedded AI/ML Capabilities: Allows integration of machine learning models for loss prediction, churn risk, and segmentation directly into workflows.
- Data Lineage & Governance: Tracks how data flows and transforms, ensuring transparency, auditability, and trust.
Why Data & Analytics Layer is Important
The data layer is not just for analysts, it underpins every major decision across product, claims, compliance, and operations. With growing regulatory scrutiny and the rise of AI-driven processes, insurers need real-time, connected, and governed data pipelines.
Checklist to Select Right Data Platforms
When assessing your data & analytics solution, consider:
- Architecture Requirements: Scalable cloud-based lakes or warehouses with support for APIs, batch/stream processing, and secure access layers for users and models.
- Functional Capabilities: Out-of-the-box dashboard templates, embedded reporting tools, real-time data ingestion, and support for custom model deployment.
- Advanced Requirements: Must support data lineage tracking, consent-based data usage, audit logs, anonymization capabilities, and integration with external benchmarks or rating bureaus.
5. How to Select the Integration Layer?
Your systems are only as powerful as how well they work together. A strong integration layer ensures seamless data flow across policy, billing, claims, portals, analytics, and external partners. It’s what enables insurers to operate as a connected ecosystem, not isolated silos.
Why the Integration Layer Matters
As insurers adopt more SaaS tools, AI services, and third-party platforms, manual handoffs and brittle point-to-point integrations become liabilities. A modern integration layer improves agility, simplifies upgrades, and accelerates digital transformation by connecting systems through reusable, scalable pipelines.
It’s especially critical for carriers adopting layered modernization, where not everything is replaced at once, and legacy + modern systems must co-exist.
Integration Layer Requirements
Your integration architecture should support:
- Support for APIs: Ability to expose and consume secure RESTful APIs for all core services (quote, bind, claim, billing, documents, etc.), with full documentation and authentication layers (OAuth2, JWT, etc.).
- Event-Driven Architecture: Publish/subscribe capability to emit real-time events to trigger downstream workflows and notifications.
- Workflow Orchestration: Ability to coordinate multi-step business processes across systems, including retries, human-in-the-loop actions, and approval flows.
- Monitoring & Observability: Centralized logging, health checks, and real-time monitoring dashboards to detect integration failures or data lags before they affect CX or compliance.
10 Common Mistakes to Avoid When Building Your Core Tech Stack
Even well-resourced insurers make strategic missteps when modernizing core systems. Avoiding these pitfalls can save years of rework, tech debt, and compliance exposure.
- Choosing Tech Without Defining Target Operating Model: Don’t start with software, start with your ideal process. Otherwise, you’ll force-fit tech into legacy workflows.
- Underestimating the Role of Data in PAS Design: Many PAS projects fail because data models aren’t structured for rating, reporting, or regulatory filings across states.
- Ignoring Claims Workflow Configurability: If business users can’t adjust claims rules or SLAs without IT, turnaround times will suffer long after go-live.
- Fragmented Billing Across Direct & Agency Channels: Running separate billing systems for agents and policyholders leads to inconsistent records, lost commissions, and reconciliation headaches.
- Treating Analytics as a Post-Implementation Add-On: Waiting to address data architecture after core rollout creates silos. Embed analytics from day one.
- Overengineering Integrations: Hard-coded point-to-point integrations are brittle and expensive to maintain. Use an API-first, event-driven approach.
- Neglecting Compliance Triggers in Core Systems: Missing state-specific cancellation rules, DOI audit logs, or rate versioning logic creates regulatory risk.
- Choosing Systems That Don't Support Layered Modernization: If your core stack can’t coexist with legacy systems during transition, the migration will stall or fail.
- Relying Only on Vendors, Not Consultants: Tech vendors sell software. Strategic insurance partners helps you design the right stack for your growth, filings, and CX goals.
- Overlooking User Experience for Internal Teams: If underwriters, adjusters, or billing teams hate the UI, adoption will lag, no matter how “modern” the backend is.
Conclusion
Whether you’re a regional carrier expanding into new states or an MGA bringing niche products to market, your success depends on choosing the right systems for policy admin, claims, billing, analytics, and integration. These aren’t isolated decisions. They shape your ability to launch compliant products, operate efficiently, and deliver exceptional service.
But building the right core stack isn’t just about selecting tools with the most features. It’s about aligning technology with your operating model, compliance strategy, and long-term business goals. It’s about ensuring each layer, from PAS to data pipelines, works together as a coordinated whole.
That’s where strategic consulting makes a difference. Partners like Practo Insura help carriers go beyond software selection, offering architecture guidance, regulatory insight, and implementation strategies tailored to U.S. P&C insurers. The result? Systems that not only work, but work for you.
How to Audit Your Current Insurance Policy Admin Process Without a Consultant
Even the most robust Policy Administration System (PAS) can quietly fall out of sync with how work gets done in the real world. Over time, teams build workarounds, bolt on spreadsheets, route approvals through inboxes, and rely on manual processes to get policies out the door. While nothing is visibly "broken," the operational drag builds: endorsements pile up, documents need correction, agents complain about delays, and compliance gaps go unnoticed until it's too late.
For U.S. P&C carriers, a regular internal audit of the policy admin process isn't just a best practice, it’s a critical step toward reducing cost-per-transaction, improving service speed, and minimizing regulatory exposure. As digital products evolve and state-level filing obligations shift, relying solely on PAS vendors or external consultants can slow your ability to act.
Content Overview
What Counts as a “Policy Admin Process”
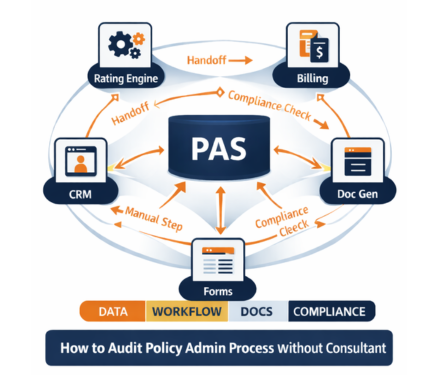
When insurers think about policy administration, they often default to the PAS itself. But a true audit needs to widen the lens. The "policy admin process" is the full set of systems, people, workflows, and artifacts that touch a policy from quote to renewal and every change in between. Here’s what should be considered in scope:
1. Core Systems: At the center are the core systems that process policy activity. This includes your PAS, rating engine, billing system, document generation, CRM, e-signature tools and portals. If these aren’t well-aligned, delays, errors, and version mismatches become common.
2. Surrounding Workflows: Surrounding these systems are the workflows that carry the real work. Manual steps like spreadsheets, shared inboxes, and on-demand approvals are often used between underwriting, servicing, billing, and compliance and are rarely captured in audits.
3. Product-Linked Dependencies: Product rules and regulatory filings also shape policy admin. You must track state-specific forms, rate versions, effective dates, and SERFF-approved changes. Poor version control here can cause downstream rating and compliance errors.
4. Compliance Artifacts: Every audit should include compliance artifacts. This means delivery of proofs for notices, form edition accuracy, and evidence of approvals. Without these, policies may appear compliant in your system but fail during regulatory review.
7-Step Policy Admin Process Audit You Can Run In-House
You don’t need a full system overhaul to uncover what’s slowing down your policy operations. This step-by-step audit helps your team identify breakdowns in workflow, handoffs, documents, and data right inside your current setup.
It’s especially useful if your policy administration system is showing signs of strain but you’re not ready for a full replacement. Use this framework to pinpoint what’s fixable now and what may need a deeper configuration review.
Step 1: Pick Your Audit Scope

Keeping the audit scope tight is important because policy admin problems usually concentrate in a few transactions, not across the entire book. Choose one or two lines of business, such as Personal Auto, Homeowners, or BOP where operational friction or volume is highest. This helps isolate issues without overwhelming your team with complexity across products or states.
Next, pick 3-5 high-impact transaction types to audit like new business, endorsements, renewals, cancellations, or reinstatements. Limit the review to one distribution channel (agent, MGA, or direct) so you can finish the audit in one to two weeks with clear, actionable insights.
Step 2: List Every System and Handoff
Start by listing all the core systems involved in processing each policy type, your PAS, rating engine, billing system, document tools, forms library, CRM, and imaging platforms. These systems often work together but rarely share data seamlessly, leading to handoff friction or duplication.
Then, identify the “shadow systems” your teams use to fill process gaps, Excel sheets, email chains, macros, or shared folders. Map out each handoff between departments and channels. If a transaction touches 4+ systems or passes through 3+ teams, delays and errors are almost guaranteed.
Step 3: Map the Real Workflow
Start with 10 real policy files and trace each from start to finish.
- Where intake happens (portal, phone, email)
- Where data is entered
- Where approvals or exceptions are handled
- When docs are generated and by whom
- Where the process stalls
This helps surface hidden inefficiencies that don’t show up in reports. Capture when documents were generated, who triggered them, and where the process slowed down or paused. SOPs often miss these friction points, but real-life samples reveal the true workflow, and where rework or delays are silently piling up.
Step 4: Measure the Baseline Numbers
To truly understand where delays and errors happen, you need to measure what’s going on. Start by tracking these 8 baseline metrics for each transaction type.
- Cycle Time - The total time from transaction intake to completion. Long cycle times often signal approval delays, missing data, or doc generation issues.
- Touches per Transaction - The number of handoffs or manual steps a transaction goes through. More touches usually mean more complexity, delays, and risk of rework.
- Rework Rate - The percentage of transactions that require corrections, resubmissions, or reissued documents. High rework is a clear sign of poor intake quality or missing rules.
- Exception Rate - How often transactions fall out of the standard processing path. Exceptions create manual work and indicate gaps in automation or rule coverage.
- First-Time-Right Documents - The percentage of transactions where documents were issued correctly the first time, with no fixes needed. This ties directly to compliance and customer trust.
- Override Frequency - How often underwriters or team members bypass system rules. Frequent overrides can point to flawed configurations or products not aligned with real-world scenarios.
- Backlog Aging - The number of open items grouped by how long they’ve been sitting. A growing backlog signals process breakdowns and bottlenecks.
- Compliance Defect Rate - The number of transactions with missing notices, incorrect forms, or invalid timing. This is critical in regulated lines and high-risk states.
Even with partial data, these will reveal hidden pain points and improvement opportunities.
Step 5: Tag Issues Using a Defect List
To fix your policy admin process, you need to track not just what went wrong but why. Tagging each issue by type helps you see patterns, assign root causes, and prioritize what to fix first.
- Data Quality - Missing or mismatched fields (like garaging address or insured name) cause rework, rating errors, and downstream doc issues.
- Rating / Version - Using the wrong version or frequent overrides often signals outdated rules or SERFF misalignment.
- Forms / Docs - Incorrect or late documents, such as outdated declaration pages or missing state forms, can lead to compliance violations.
- Workflow - Stalled queues or unclear ownership often cause silent delays and force teams to escalate or work outside the system.
- Billing - Errors like wrong proration, fee mismatches, or missed reinstatement syncs stem from poor PAS-billing coordination.
- Compliance - Late or missing notices, wrong form editions, or no delivery proof pose regulatory risk, especially in states like California (Prop 103).
Tracking these defects helps separate small inefficiencies from high-risk issues, and ensures your fixes reduce both rework and regulatory exposure.
Step 6: Score Your Maturity
To turn your audit findings into action, rate your policy admin process across six core dimensions using a simple 1-5 scale. This helps you visualize weak spots and prioritize what to fix first especially when time and resources are limited.
- Process Clarity: Are the steps clearly defined, consistently followed, and assigned to specific owners?
- Automation Coverage: Are routing, validations, and decisions rule-based, or do they depend on people to catch things?
- Data Integrity: Is there one source of truth for policy data, or do users re-enter info across systems?
- Document Control: Are forms issued with the right version, timing, and audit trail?
- Compliance Resilience: Can you prove that required notices, approvals, and overrides were completed and documented?
- Change Readiness: Can you roll out rate/form changes without breaking workflows or triggering confusion?
Sample Heatmap (for Auto Endorsements)
| Category | Score (1-5) | Notes |
|---|---|---|
| Process Clarity | 2 | Steps vary by representation, no shared checklist |
| Automation Coverage | 1 | Manual routing and approvals for nearly all changes |
| Data Integrity | 2 | Re-keying in PAS and billing system |
| Document Control | 3 | Some automation, but forms often corrected manually |
| Compliance Resilience | 2 | Delivery evidence and overrides not consistently logged |
| Change Readiness | 1 | Rate updates cause downstream issues in billing/docs |
Tip: Start fixing the areas where your score is 1 or 2. You’ll get the biggest impact with the lowest resistance and build momentum for broader changes.
Step 7: Build a Prioritized Fix List
Once you've mapped your issues, scored your maturity, and measured your metrics, it's time to act. But not everything needs a full-scale project. Sort fixes into Quick Wins, Medium-Term Improvements, and Strategic Initiatives based on how hard they are to implement vs. the value they’ll deliver.
A smart prioritization prevents teams from getting stuck in analysis or chasing low-impact fixes first.
Quick Wins (2-6 weeks)
These are low-effort changes that can be implemented by operations or product teams without system overhaul.
- Mandatory Field Validations: Add rules to prevent incomplete or inconsistent data at intake (e.g., missing driver info or vehicle use).
- Queue Assignments and Routing Rules: Standardize who handles what, no more bouncing between inboxes or shared folders.
- Doc Trigger Timing: Shift document generation earlier in the process to avoid last-minute errors or corrections.
Why it matters: These fixes reduce rework and cycle time fast and build confidence across teams.
Related Read: How to Enter New P&C Markets Without a Core Overhaul
Medium-Term Fixes (6-12 weeks)
These need some cross-functional effort or minor configuration but are achievable without a full system redesign.
- Rules-Based Triage: Automatically assign work based on type, geography, or LOB to reduce backlog and manual routing.
- Renewal Automation: Apply rules to auto-process clean renewals (e.g., no MVR change, no claims), increasing Straight-Through Processing rates.
- Approval Capture Updates: Move approvals and exception logging out of email and into your core system, with full audit trail.
Why it matters: These fixes increase consistency and visibility while freeing up capacity for complex cases.
Strategic Initiatives (90+ days)
These require significant IT involvement, vendor coordination, or budget, but solve core system or integration pain.
- PAS Configuration Redesign: Rebuild outdated workflows, endorsement types, or rating logic that no longer serve your product needs.
- Event-Driven Integrations: Replace batch file transfers or manual triggers with real-time data sync across PAS, billing, and forms.
- Workflow Engine Upgrades: Implement or modernize tools that support dynamic routing, SLAs, and task visibility across teams.
Why it matters: Strategic fixes unlock long-term agility, especially if you're expanding to new products or states.
Attach each fix to a KPI improvement (e.g., reduce endorsement cycle time by 2 days, cut rework rate by 20%). This helps you track ROI and build a case for ongoing optimization.
3 Things to Do After the Audit
1. Align the Team on Priorities and One Metric
Once your audit findings are in, first, align your team on what matters most. Share a simple summary: the top issue you uncovered (e.g., delays in endorsement processing), the most common defect type (e.g., missing approval evidence), and one clear metric to improve (like reducing endorsement cycle time by 20%).
This gives your team a shared target and avoids scattered efforts. Keeping the focus tight builds early momentum and makes success measurable.
2. Build Your Roadmap from Audit Evidence
Turn your audit findings into an actionable improvement plan. Start by grouping the fixes into clear categories so teams know where they fit and what they’re solving for.
Assign each fix an owner and a realistic deadline. Begin with quick wins that can be delivered in 2-6 weeks to build momentum and show immediate impact. Then phase in medium and strategic fixes based on effort and dependency.
A roadmap grounded in real audit evidence, keeps teams focused, accountable, and aligned with business priorities.
3. Create a Dashboard to Track KPIs
Build a simple dashboard using the 8 baseline metrics from your audit: cycle time, touches, rework, exceptions, doc accuracy, override rate, backlog aging, and compliance defects. Even a basic Excel or BI tool setup works if it gives visibility.
Update the dashboard weekly or biweekly so teams can spot trends early and adjust. Highlight any spikes in exception rate, rework, or backlog, which often signal workflow breakdowns, product rule gaps, or upcoming compliance risk.
When to Bring Help
While many fixes uncovered in your audit can be handled internally, some challenges point to deeper structural issues that need outside support. Knowing when to bring in an expert strategic insurance consulting partner like Practo Insura can help save time, reduce risk, and prevent your team from patching over problems that need strategic change.
- Repeat compliance defects tied to state rules: If you’re consistently missing notice timing or form requirements (e.g., Prop 103 in California), the risk is too high to manage with patchwork fixes.
- You can’t measure key performance metrics: When systems are fragmented and data is scattered, you lose visibility and that makes both improvement and compliance nearly impossible.
- Your PAS needs workarounds for every product change: If launching new products or states requires manual overrides and config debt, it’s time to rethink your platform strategy.
- Exception handling is mostly manual: When approvals and corrections happen over email, not in-system, you're exposed to audit gaps and operational slowdowns.
- Expansion plans will strain your workflows: If your current process can’t keep up today, adding more states or products will only magnify the problems.
Conclusion
You don’t need a consultant or full system replacement to understand what’s slowing down your policy operations. A focused in-house audit can show you:
- Where handoffs, errors, and delays happen
- Which metrics matter most (and where you’re blind)
- What fixes are fast and what needs long-term planning
But an audit won’t fix broken configurations, outdated rating models, or multi-system gaps between forms, rates, and workflows. It won’t guide you through state expansion complexity or modernize how you execute changes across lines of business.
Practo Insura helps P&C carriers translate audits into action. Whether you’re launching a new product, reworking your PAS config, or untangling compliance issues across 10+ states, we bring the execution support to match your intent with speed, structure, and industry depth.
10 Reasons Why State Expansion Fails for P&C Carriers in USA
For many P&C carriers, expanding into a new state seems straightforward: file the product, turn on quoting, and go live. But in reality, state expansion is a full system rebuild, impacting rate filings, underwriting rules, servicing workflows, compliance protocols, and claims readiness.
It’s not a one-time launch. It’s an ongoing effort to meet each state’s regulatory, legal, and operational demands. In fact, according to a survey, carriers expanding into new jurisdictions report up to 30-35% more regulatory objections and measurable increases in claims cycle time and loss adjustment expenses, mostly due to operational gaps, not filing errors.
3 Types of Delays That Break State Expansion
Even with a greenlit filing and a go-live date, most state expansions start to fracture not at the product level, but at the operational, regulatory, and risk layer post-launch.
These breakdowns fall into three main categories: preventable failures, controllable pressures, and non-preventable forces. Understanding the difference is key to building an expansion plan that holds up once the quoting begins.
1. Preventable Failures (Execution Gaps)
These are internal breakdowns that stem from poor planning, weak filing execution, or lack of operational readiness. They’re the most fixable, but often the most overlooked.
For example, submitting an incomplete SERFF package in California or missing transmittal forms in New York can delay approvals by months. Likewise, failing to stand up state-specific claims or notice templates can lead to compliance issues and service friction from day one.
Preventable failures also include launching without a clear ROI model or choosing states with poor data credibility, which can lead to profitability loss within the first 90 days. These risks are fully avoidable with the right governance, documentation, and readiness checklist.
2. Controllable Pressures (Manageable Trends)
These delays don’t originate inside your team, but you can control how much they affect your performance.
Take repair inflation: carriers across the U.S. have seen labor and parts costs rise 31% in Q1 2025, especially for vehicles with ADAS (advanced driver assistance systems). You can’t stop inflation, but you can build inflation buffers into pricing, negotiate preferred vendor contracts, and monitor claim severity trends early.
Another example is the lag between pricing and loss experience in prior-approval states. In short, controllable pressures aren’t your fault, but they are your responsibility.
3. Non-Preventable Forces (Market Shocks)
Some expansion problems have nothing to do with execution or strategy. They’re simply market shocks that no carrier, big or small, can avoid.
Wildfire exposure in California, hurricane season volatility in the Southeast, or a reinsurance pricing spike can change the math on an entire state's viability overnight. Even well-run programs can become unsustainable when CAT concentration or capital availability shifts.
In these cases, resilience planning and fast pullback governance are your only defenses. The key here isn’t control, its readiness.
5 Preventable Mistakes That Derail P&C State Expansion
1. Filing Quality Gaps Create Rework and Delays
In a multi-state expansion, your rate and form filings aren’t just documentation, they’re the entry point to market participation. Yet many carriers approach them with a back-office mindset, assuming that what worked in one state will fly in another. That’s where expansion starts to crack.
In reality, SERFF filings are highly state-specific, and regulators are quick to reject filings that don’t follow precise formatting, justification depth, or form language. In prior-approval states like California (CA DOI) and New York (NY DFS), filings may require multi-layered actuarial support, exposure-based rate breakdowns, and specific consumer notice language.
How to Prevent It
- Standardize your SERFF packages with modular templates and naming conventions.
- Maintain state-specific pre-flight checklists to ensure all transmittals and exhibits meet current DOI rules.
- Build an objection playbook with sample responses and previous objection themes.
- Assign filing owners and respond to SLAs to avoid delayed DOI interactions.
- Use a dashboard to track filing stage, objection count, and approval status across states.
Related Read: How Practo Insura Helps Carriers Navigate Multi-State Compliance
2. DOI Objections Stall Momentum Without Clear Ownership
Objections aren’t failures, they’re part of the regulatory dialogue. But in multi-state expansion, carriers often fail to respond quickly or consistently, especially when ownership is unclear. A single unresolved objection can stall approval for weeks and create rework across rate, form, and underwriting files.
Each state has different review styles: while Florida may focus on rating adequacy, Pennsylvania may zero in on underwriting eligibility. Without a formal objection-handling system, even well-prepared filings can spiral into 60+ day delays. Carriers that lack defined SLAs and documentation discipline often find themselves resubmitting multiple versions.
How to Prevent Objection-Driven Delays
- Assign clear response owners by function (forms, actuarial, legal, compliance)
- Track objections centrally across filings and states
- Use pre-approved response templates for common objection themes
- Set internal response SLAs (e.g., <5 business days per objection)
- Build an objection resolution log for faster future responses
3. Weak Expansion Gating Leads to Bad State Choices
Too often, carriers expand into new states based on market size or executive preference, without fully evaluating regulatory friction, loss volatility, or cost to serve. This leads to avoidable missteps, especially in states with high catastrophe risk or aggressive DOI scrutiny.
For example, launching in Louisiana or Florida without modeling reinsurance cost, litigation risk, or CAT exposure can undermine even well-priced products. Many carriers underestimate how fast claims frequency and cycle time escalate in complex states.
How to Prevent Strategic Misfires
- Score every target state with a readiness matrix (filing, claims, risk, distribution)
- Assess CAT exposure, reinsurance terms, and DOI timelines
- Model different mix scenarios (segment, geography, peril) pre-launch
- Gate expansion on a multi-team signoff (product, compliance, ops, actuarial)
- Pilot narrow before statewide rollout
Read More: 5 Questions Carriers Must Ask Before Launching a New Line of Business
4. Claims Operations Aren’t Ready for Local Reality
Filing success doesn’t guarantee servicing success. Many carriers expand without building state-specific claims infrastructure, from vendor networks to repair timelines. The result? Longer cycle times, higher LAE, and rising complaint volumes.
States vary widely in how claims unfold. For example, BI litigation frequency in Texas or medical escalation in New York can significantly increase severity. Without localized playbooks and pre-vetted vendors, carriers struggle to meet SLAs or control severity.
How to Build Claims Readiness
- Onboard vendors before launch (IA (Independent Adjuster), repair, rental, legal)
- Create state-specific claims handling playbooks
- Monitor cycle time and LAE by region from week 1
- Define escalation workflows for attorney-represented claims
- Train adjusters on regional norms and regulator expectations
Related Read: Why Strategy Comes Before Software in Insurance Modernization
5. Severity Controls Fail Without a Total-Loss and ADAS Strategy
Severity issues are predictable and preventable. Many expansion efforts break down because carriers don’t update their total-loss strategy or repair assumptions for newer vehicles.
ADAS-equipped cars cost more to repair, and parts delays increase cycle time. In states with high total-loss frequency, lack of calibrated thresholds leads to overspending. Carriers also miss salvage value recovery opportunities due to slow or inconsistent total-loss handling.
How to Control Severity Early
- Update total-loss thresholds by vehicle type and state
- Train adjusters on ADAS (Advanced Driver Assistance Systems) repair and recalibration
- Monitor severity per claim type from week 1
- Use predictive tools for settlement decisions
- Improve salvage vendor contracts and pickup timelines
3 Controllable Factors That Derail Expansion
1. Repair and Replacement Costs Rise Faster Than Assumptions
Even when frequency is stable, many state expansions fail because repair and replacement costs accelerate faster than pricing assumptions. Labor shortages, parts inflation, longer repair cycles, and ADAS recalibration have materially increased average paid losses, especially in metro-heavy states.
According to the U.S. Bureau of Labor Statistics, auto repair and maintenance costs rose by roughly 30% between January 2020 and November 2024, while used vehicle values remain elevated, pushing more claims into total-loss territory. In new states, carriers often rely on historical severity assumptions that don’t reflect local repair economics, leading to early loss-ratio deterioration.
How to Control the Impact
- Build higher severity buffers into initial pricing assumptions
- Segment pricing by vehicle type, geography, and repair complexity
- Establish preferred shop and parts sourcing networks early
- Track severity drift weekly in the first 90 days
- Adjust appetite quickly if early loss signals exceed thresholds
2. Crash Severity Increases Even When Volume Doesn’t
In many states, accident frequency has stabilized, but crash severity continues to climb. Faster vehicles, distracted driving, higher medical costs, and litigation intensity all contribute to larger bodily injury and property damage claims.
This trend is particularly visible in states with dense traffic, higher speed limits, or aggressive plaintiff environments. For carriers entering new markets, severity trends often diverge from national averages, making early experience look worse than expected, even without a spike in claim counts.
How to Control the Impact
- Refine underwriting by zip code and driver profile
- Apply tighter eligibility and coverage limits in high-severity areas
- Monitor BI severity separately from frequency metrics
- Use early-warning dashboards to detect severity spikes
- Adjust underwriting rules before losses compound
3. Pricing Lags Behind Loss Trend in New States
In prior-approval states, carriers often face a timing mismatch between loss experience and pricing action. Even when data shows rising severity or mix shift, rate changes can take months to approve, leaving carriers exposed during the gap.
This lag is especially risky in new states, where early experience is still forming and small deviations can quickly compound. Without built-in pricing flexibility, carriers are forced to absorb losses longer than planned.
How to Control the Impact
- File rates with deductible, tier, and coverage flexibility
- Use underwriting and eligibility levers while rates are pending
- Monitor quote-to-bind and loss trends weekly
- Prepare rate refiles earlier than historically planned
- Limit growth until pricing stabilizes
Related Read: How to Break Product Stagnation with Insurance Strategic Consulting
2 External Factors for State Expansion Delay You Can’t Control
1. Catastrophe Volatility Reshapes Exposure Overnight
Some expansion setbacks have nothing to do with execution. Catastrophe volatility like wildfires, hurricanes, floods, hail, and secondary perils, can alter a state’s risk profile almost overnight. Even well-priced, well-managed products can become unviable when loss concentration spikes unexpectedly.
For example, carriers expanding into states like California, Florida, or Texas may face sudden shifts in exposure due to wildfire seasons or storm frequency, often mid-policy year. These events are non-preventable and frequently exceed modeled expectations, forcing carriers to reassess appetite, underwriting limits, and growth plans in real time.
What Can Be Done After the Catastrophe
- Reassess geographic concentration and exposure limits quickly
- Adjust underwriting and growth controls post-event
- Revisit reinsurance layers and CAT retention assumptions
2. Reinsurance and Capital Cycles Change the Economics
Reinsurance availability and pricing are external forces that carriers simply cannot control. A shift in reinsurer appetite, higher attachment points, or sudden price increases can materially change the viability of a state expansion, even after a successful launch.
In recent renewal cycles, many carriers saw reinsurance costs rise sharply or capacity tighten, particularly in catastrophe-exposed states. For some, this forced difficult decisions: slow growth, reduce exposure, or exit markets despite otherwise sound underwriting and operations.
What Can Be Done After the Fact
- Reevaluate growth targets based on updated reinsurance economics
- Optimize retention and layering strategies
- Align capital allocation with revised risk appetite
Conclusion
State expansion isn’t just about entering new markets, it’s about withstanding new pressures. Most failures don’t occur at the filing stage but after launch, when claims, compliance, pricing, and servicing are tested simultaneously. While some risks like CAT volatility or reinsurance pricing are out of your hands, many setbacks stem from preventable gaps: mismatched filings, unmanaged objections, underprepared claims operations, or outdated pricing assumptions.
That’s why more carriers are turning to an insurance strategic consultant to guide strategic expansion with discipline, not just speed. At Practo Insura, we help P&C insurers build scalable expansion strategies from multi-state filing execution to product modularity, state-readiness scoring, and post-launch monitoring.